Within Network Security & Support roles it’s normal practice to, at some point, have to jump onto a CLI and start messing around with tcpdump.
For me it’s usually when there’s a connectivity issues either between two hosts, i.e. server/client or server/server. That’s where TCPDUMP is a massive help, as packets don’t lie. If you can show said server/developer bod, in black and white what is going on, they can’t argues – although they still may. 😉
If I had a penny for every time a colleague blamed a firewall or the network for why their server isn’t communicating as it should, I’d be a wealthy man.
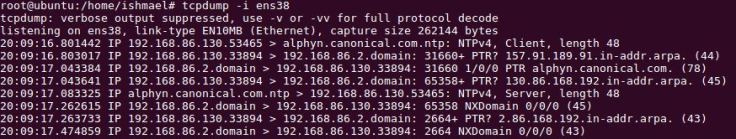
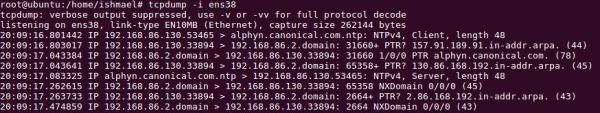
Below are some of my most frequently utilised tcpdump commands and switches, and what they do and print.
My Favourite TCPDUMP Commands
tcpdump -i any host 10.1.1.1 and host 10.2.2.2
This is a good starter to see all traffic between two hosts. After you’ve confirmed you’re receiving output you can then look to add further switches to filter further.
Useful Switches
tcpdump -D shows the interfaces you can capture on
tcpdump -i any will capture traffic on all available interfaces
Use -c to stop your tcpdump after a specific number of packets have been captured
To display IPs and not hostnames use the -n switch
The default packet capture byte size is 65535, i.e. the full packet, therefore if you only want to capture the first 64 or 96 bytes of each packet, use the -s switch
-S will turn off relative sequence numbers and give you the complete, harder to read strings
Use the -w <filename>.pcap to write a capture to a file, but use -v to display how many packets have been captured to file.
You can view your written capture files on the CLI, however they display just the same, therefore I prefer to review them in Wireshark.
That’s a whole series of blog posts in itself though, happy capturing 🙂
I.